Domain Driven Architecture
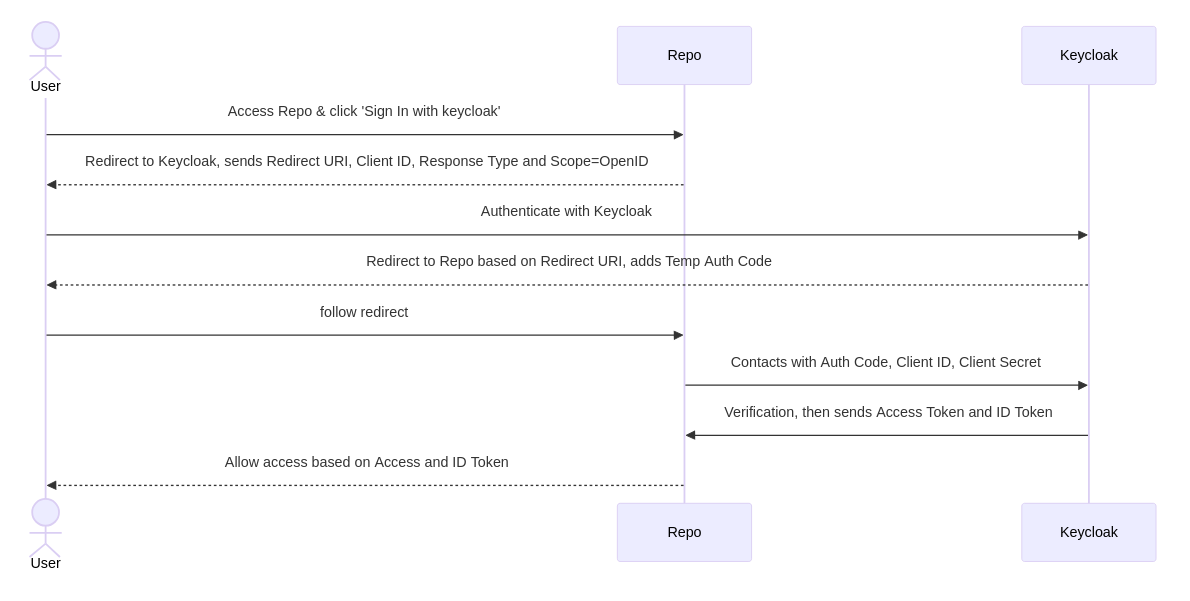
Keycloak OpenID connect authentication allows users to log in to Forgejo using their Keycloak credentials. This HowTo explains how to set up Keycloak as an authentication provider in Forgejo.
Authentication
First usecase to integrate is authentication. Authentication tells the integrated Forgejo who the user is. Under the hood this will login existing users and in addition register unknown ones.
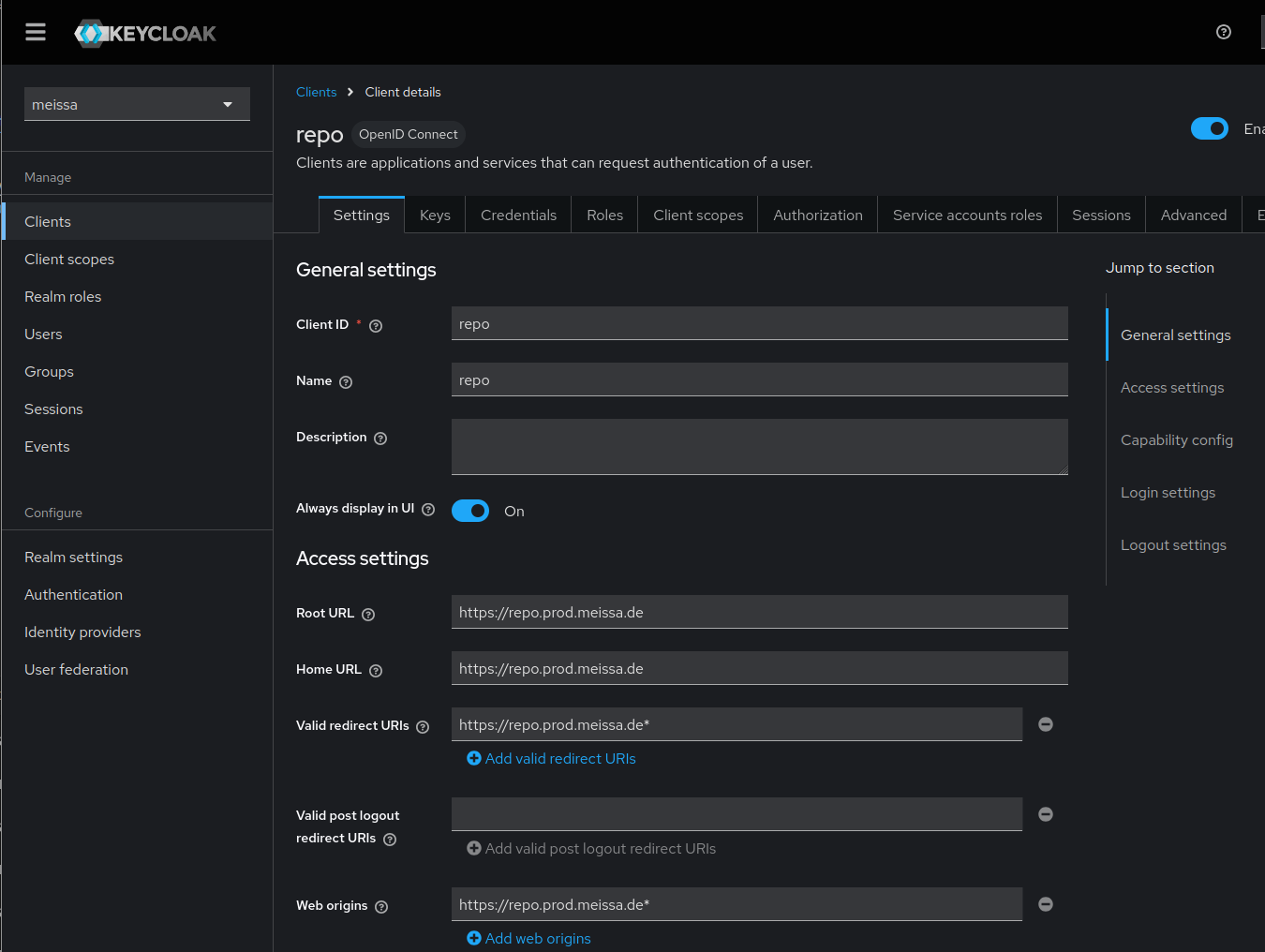
Keycloak configuration
- login as realm admin (for keycloak newbies
https://[your.keycloak.server]/admin/[your-realm]/consoleis a good guess) - create forgejo-client
- Client authentication:
on - Root URL:
[https://your.forgejo.server] - Home URL:
[https://your.forgejo.server] - Valid Redirect URLs:
[https://your.forgejo.server]*
- Client authentication:
- create a testuser to test keycloak integration
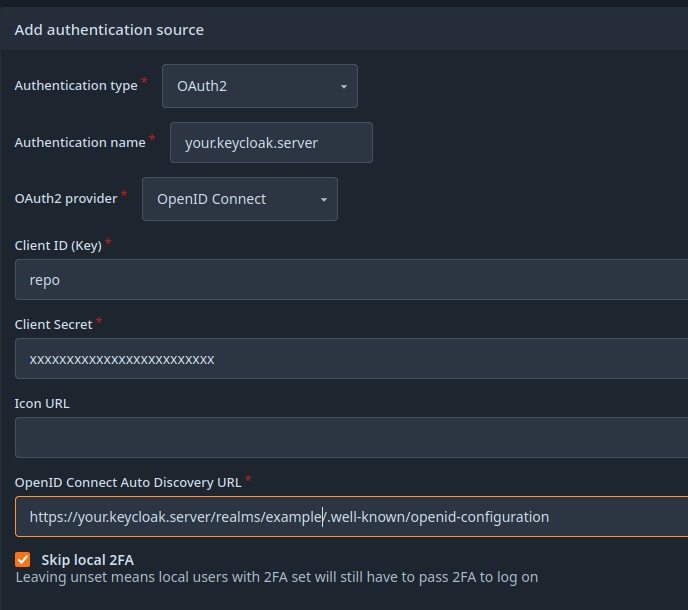
Forgejo configuration
- login as Forgejo admin
- navigate to Site administration -> Identity & access -> Authentication sources
- Add authentication source
- choose OpenID connect
- copy Client secret from keycloak to Forgejo
- enter the OpenID Connect Auto Discovery URL:
https://[your.keycloak.server]/realms/[your-realm]/.well-known/openid-configuration - Skip local 2FA:
on
Authorization or role, org & team sync
Authorization in Forgejo happens based on some predefined roles and on organization & team membership. If we maintain groups in keycloak the mapping of groups to Forgejo (organization x team) combinations is supported.
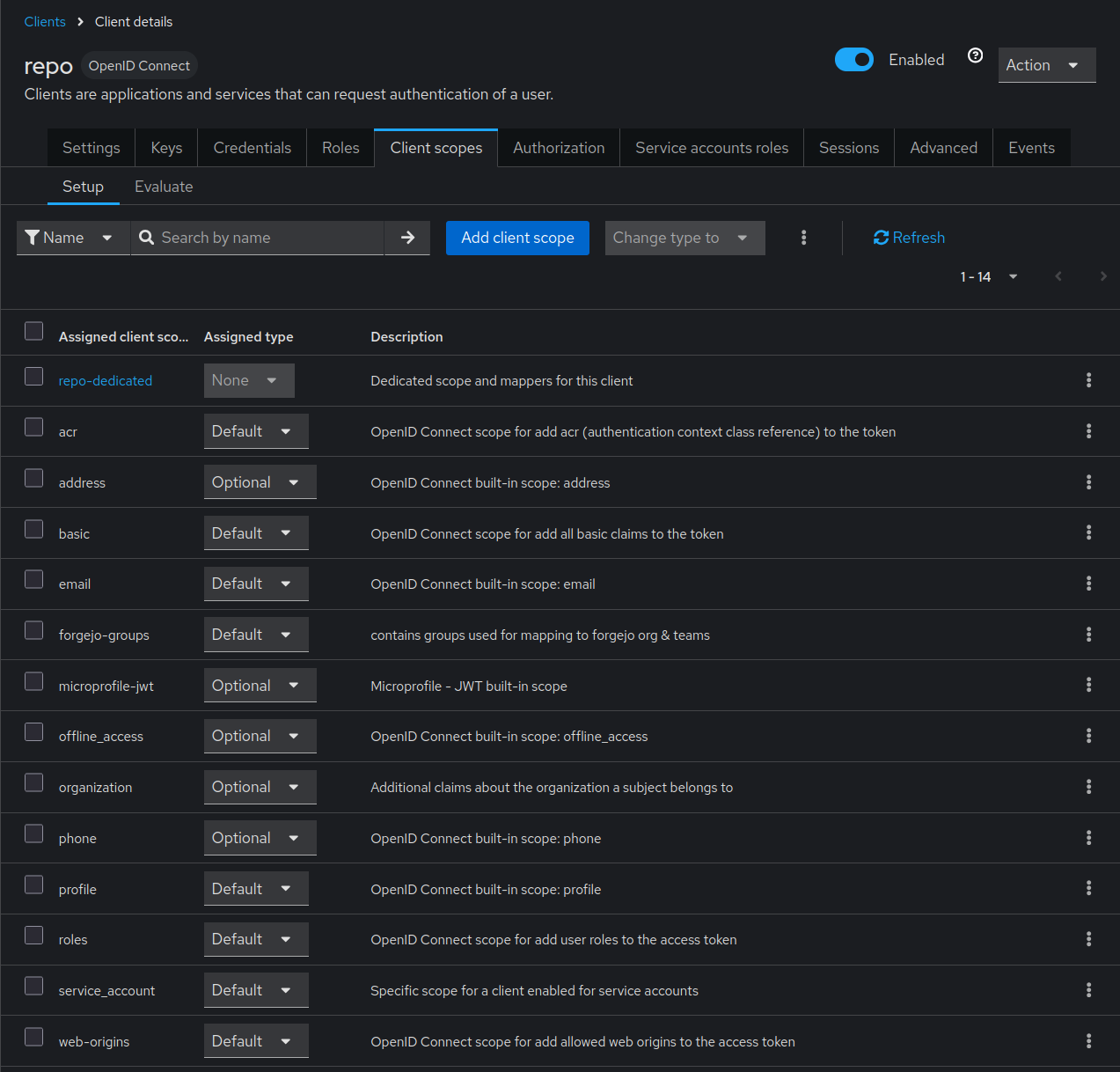
Keycloak configuration
- Create a client scope
- Set Name to e.g.
forgejo-groups - Leave Type at
None Save
- Set Name to e.g.
- Click Mappers
- Click Configure a new mapper
- Click Group Membership
- Set Name to e.g.
forgejo-groups - Set Token Claim Name to e.g.
forgejo-groups. This is a value, that needs to be set in Forgejo. - Unset Full group path. For our example we use the plain group names.
- Make Sure Add to ID token, Add to access token, Add to userinfo are set.
Save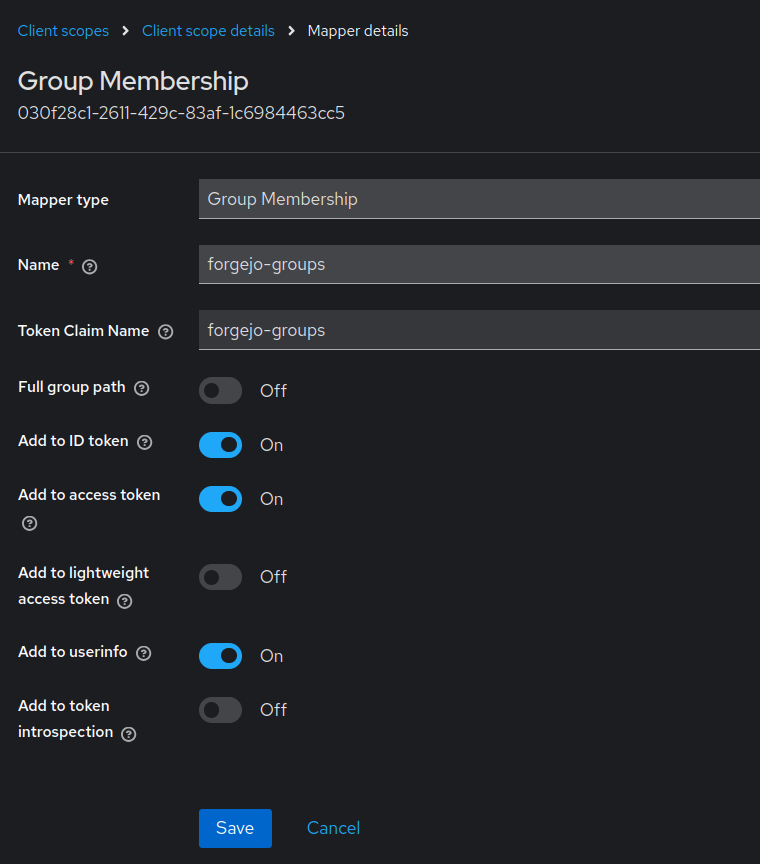
- Go to Groups
- Create groups and respective sub-groups. The group names need to be set in Forgejo
- Add users to their respective group/sub-groups. The users will be added to teams of the same name in existing organizations in Forgejo.
- Go to Clients
Forgejo configuration
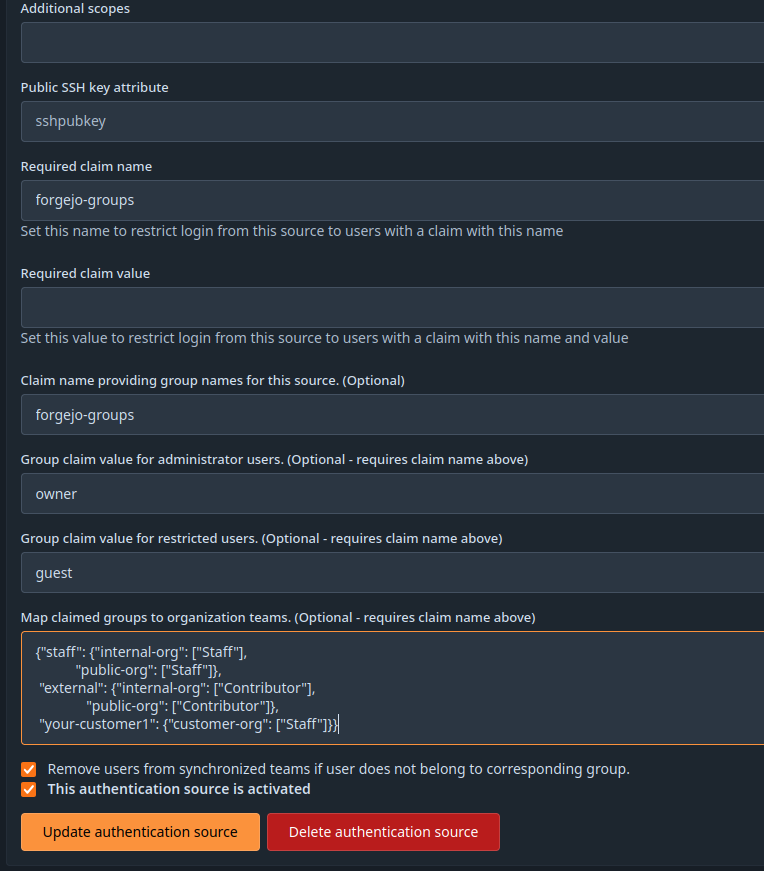
- navigate to Authentication source created above.
- Set Claim name providing group names for this source. (Optional). Must be the same as
Token Claim Name - Set Group claim value for administrator users. if desired. Must be the name of the keycloak group you defined to be administrator group.
- Set Group claim value for restricted users if desired. Must be the name you chose for the restricted access in keycloak.
- Add the mapping in Map claimed groups to organization teams.. The mapping might look like
{"staff": {"internal-org": ["Staff"], "public-org": ["Staff"]}, "external": {"internal-org": ["Contributor"], "public-org": ["Contributor"]}, "your-customer1": {"customer-org": ["Staff"]}} - Optional: Check the Remove users from synchronized teams if user does not belong to corresponding group. box for synchronized teams. This will remove users from a role / team if they are removed on keycloak side. Be careful! If you screw up your mapping, the role- and team-membership will also be removed.
- Set Claim name providing group names for this source. (Optional). Must be the same as
The sync is done on next user login or session renew.
Logout Integration
At the moment there is
- no Single Logout. That means if a loged in user presses logout in forgejo, forgejo will not inform keycloak about the logout happened.
- no Logout Hook in Forgejo. That means keycloak can not active log out a user which is logged / deactivated out in keycloak. To reduce the impact you may configure a short session timeout:
[session] SESSION_LIFE_TIME = 3600